What We Saw At the 2026 National Planning Conference
We just got back from the 2026 National Planning Conference in Detroit, where we spent most of the week walking the floor, listening to different...

Explore our 2024 comparative review, your ultimate guide through the top-tier plan review solutions.
2 min read
e-PlanSoft™ Team Mar 16, 2022 3:40:00 AM

Ransomware attacks are on the rise as the number of internet users continue to increase due to the pandemic. Although cybercriminals have been around as long as the world wide web, attacks have become more common starting in mid-2020 – when cybercriminals were given a wider target and began to launch attacks using COVID-19 related information as bait. These attacks can gain access to networks in many forms, including PDF files or links for the intended target to click. They contain malicious software (malware) that block the victim’s access into their own network and data until the attackers are paid a ransom, generally a large sum of money or cryptocurrency, to unlock the data. Cryptocurrency is quickly becoming the preferred form of ransom as it provides greater anonymity for the attackers.
Recently, cyber-attacks have been ramping up and public sector agencies are among the primary targets; putting them out of commission for weeks, or even months, while they work to regain access to their files. Public sector agency attacks are on the rise likely due to their storage of highly sensitive information and the perception that they may not be as diligent to keep their antivirus technology perpetually up to date. Network-based programs have been isolated in ransomware attacks – losing important data and risking the integrity of the data once retrieved by the user again.
– Host your data in the cloud environment with the top rating for security. Cloud-based environments are common in organizations to provide an extra layer on top of anti-virus software.
– Ensure you are using a cybersecurity program and update your anti-virus software routinely.
– Train staff on security risks, including how to identify a suspicious email or attachment and other entries into the agency network.
– Ensure that your cloud host backs up your data at regular intervals. In the event malware has infiltrated your system, your data will be secure and saved to redownload onto your server.
In 2022, there are a reported 7,500+ government agencies using AWS (Amazon Web Services) to host their most secure and sensitive data. In addition to other considerations, the choice was made to gain an extra layer of security and reliability for their constituents. AWS is the leading provider of cloud-based hosting that has put safeguards in place to ensure that data is secure and risks will be detected and resolved immediately.
Reclaiming control of the network and data isn’t easy after a cyber-attack. It often takes a full staff of IT professionals anywhere from several days to weeks to manually reboot the system and remedy the issue, even if the data has been backed up outside of the agency’s network. Data stored in the cloud is encrypted to supply a secondary layer of security for its users. Organizations with AWS cloud-based platforms are increasing due to the ironclad protection of their important data.
According to GovTech.com, hackers discovered vulnerabilities to software applications used by more than 18 United States government agencies and were able to implant malware in their systems. Research is still being conducted and data is still being collected, but it is estimated that six states have been affected by this attack called LOG4J between May 2021 and February 2022. Are you prepared in case cybercriminals attack your server or applications?
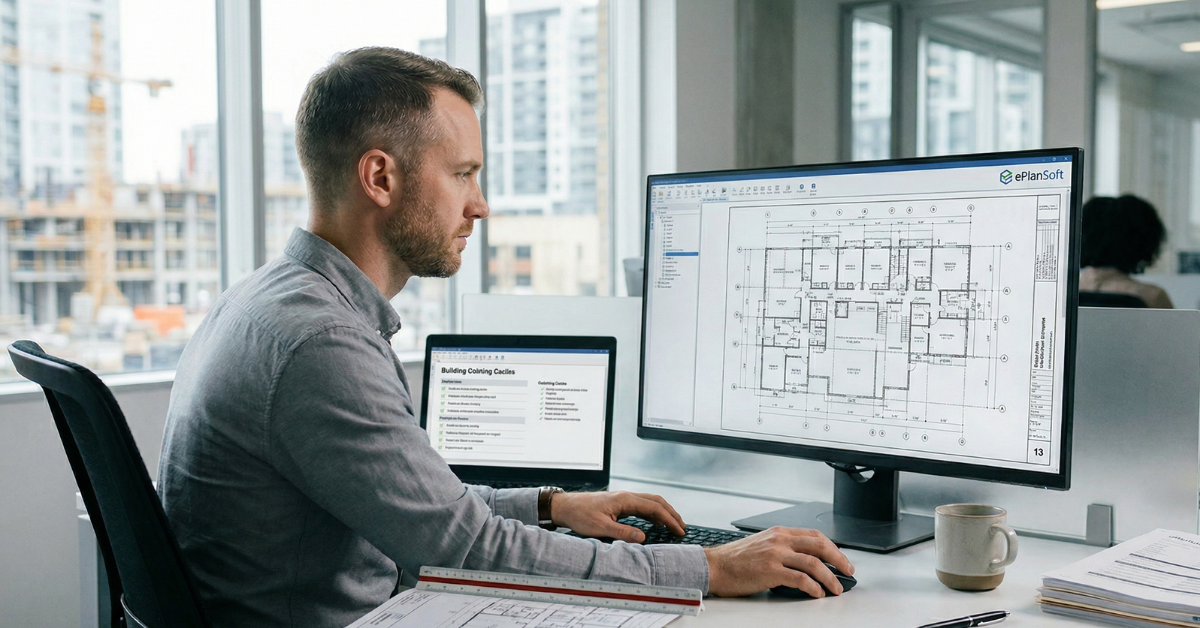
If your agency is using a network-based platform for electronic plan reviews, it’s important to recognize the risk of a ransomware attack for your agency at risk. Government agencies are protected by using e-PlanREVIEW®! e-PlanSoft’s solutions are hosted in the leading, most secure cloud-based AWS platform. Together, AWS and e-PlanREVIEW, not only assist government agencies and organizations in reducing vulnerability to ransomware attacks, but also proves to be cost-efficient when noting that less ransomware attacks will be paid, and less time out of commission due to time spent retrieving and hacked data, than when using a network-based platform.
Want to see it for yourself? Request a demo to see how much more efficient and protected your operations can be with e-PlanREVIEW.

We just got back from the 2026 National Planning Conference in Detroit, where we spent most of the week walking the floor, listening to different...

In the world of building department workflow software, there is a pattern we’ve noticed across agencies of all sizes. When resubmittal cycles...
There's a lot of conversation in the plan review world right now about AI. What it can do, what it can't, and what's coming next. (By the way, we're...

FOR IMMEDIATE RELEASE
FOR IMMEDIATE RELEASE

Every day, more organizations rely on cloud-based SaaS instead of on-premise products and services to operate efficiently, effectively, and with...